The exploits of a young Don Juan : Apollinaire, Guillaume, 1880-1918 : Free Download, Borrow, and Streaming : Internet Archive

Apple declines to fix vulnerability in Safari's Web Archive files, likely because it requires user action to exploit | iMore

Edward's Exploit and Other Thomas the Tank Engine Stories (1993 Paperback Book) : Random House : Free Download, Borrow, and Streaming : Internet Archive
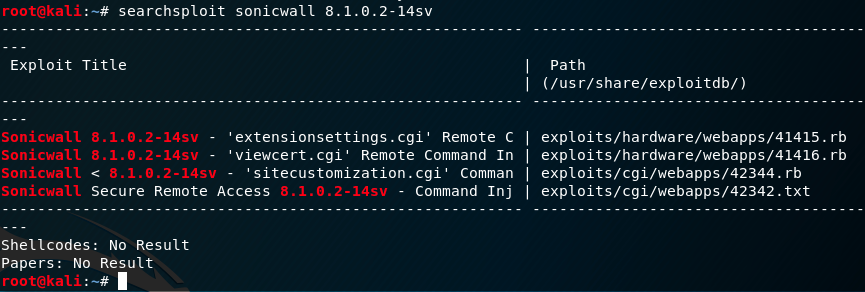
GitHub - yaph/exploit-db-archive: Script to process data from the Exploit database for later visualization with D3
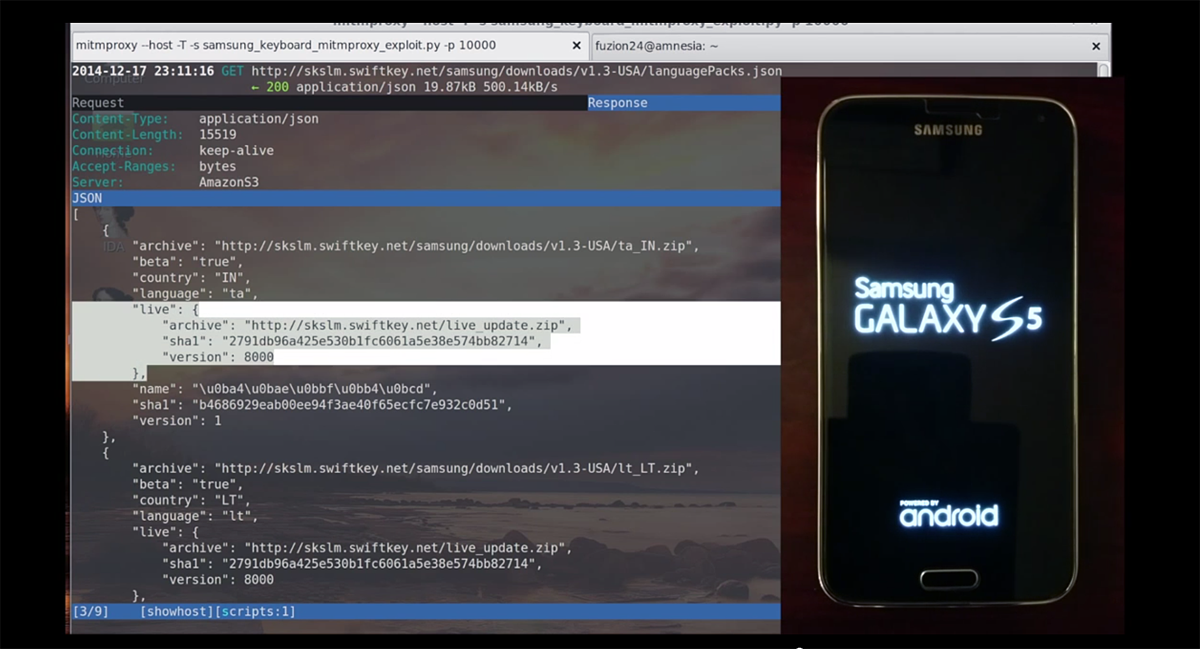
GitHub - The-Gopro336-Archive/PSA-MINERCRAFT-RCE-EXPLOIT: Minecraft exploit allowing remote code execution via Minecraft chat